Scenario
You have an Internet system that you would like to administer remotely without leaving the administrative service open to the entire Internet. However you’re not always coming from the same source IP address. Although it’s common practice to restrict access to only secure administration services (eg SSH) I’d like to avoid having any TCP ports exposed to the open Internet.
My specific scenario is this. I have a VPS hosted in the cloud which I don’t want to have ANY ports open to would be attackers. I wish to manage the server via SSH but again I don’t want to even have this port open to the entire Internet. Thus we need a way to firewall our VPS off from the entire Internet and yet easily open access to ssh from any IP address. To make this easy it should not require a dedicated client and should hopefully use a standard and easy method to send the password.
Solution
Enter SimSim, which can be downloaded at http://leetsys.com/programs/simsim/v1.0/. SimSim monitors network traffic using libpcap. If it sees the configured ‘password’ come in on any UDP packet it will execute a defined script. In our case the defined script modifies iptables to allow any TCP connection from the IP Address of the packet that contained the password. However it can really execute any command we want as it’s just a simple call to system().
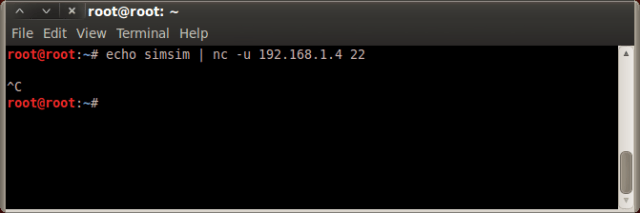
To trigger the password we simply use netcat with the -u (for UDP) option and include the password. The default password is simsim which is defined in simsim.c. To take up fewer system resources (CPU & Memory) simsim currently only monitors UDP port 22, which means we’ll rarely be inspecting packets that are not in fact sent by us. This of course can be changed by changing the BPF filter in simsim.c.
Example
Let’s take a look at an example of simsim in action.
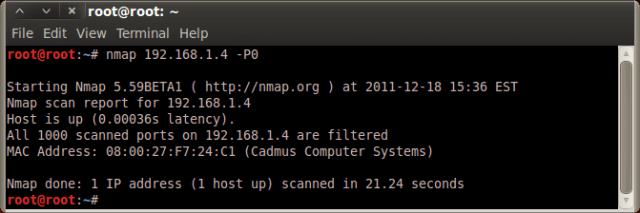
First we start by port scanning our target server running simsim.
You can see that our server has no open ports. Next we send the server the configured password via netcat on port 22.
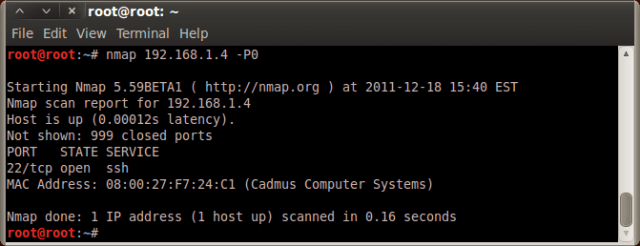
We then portscan the server again and voila, we see that we can access the SSH server.
Shortcomings
There are of course a few shortcomings in this design. The biggest of which is the fact that the password is sent in cleartext with no cryptographic exchange by the server. When you take into account what simsim is designed to do and who it’s meant to keep out this seems like an acceptable risk to me. We could design a more robust solution but then it would require a dedicated client to be used vs using netcat which is widely available today.
We’re assuming that we are on a trustworthy network connection and that we’re more worried about attackers coming from other areas of the Internet. Likewise if someone were to capture the password via sniffing and replay the packet they would be able to trigger simsim into executing the defined script. This again is not such a big deal as they still need to authenticate to the SSH deamon. As long as you don’t use the same password to trigger simsim as you do to log in to your SSH deamon you should be fine.
Flexibility
Because we can execute any system command the options are limitless for what we could have simsim do in reaction to receiving the identified password, we could potentially even setup multiple ‘passwords’ to trigger different events. This could even be used as a potential backdoor. Imagine a situation where you could add a user account or change the root password remotely by sending a single UDP packet!
Good job. I hope to have the expertise one day. astonished to have found a web log
the great.
LMAO, this is clearly spam but way too funny not to approve it. Thanks for the ego boost spambot.